For Finance, Ops & Admin Leaders in PA, NJ & DE Managing IT by Default
If you’re the one fielding IT questions, approving vendor renewals, or managing tech support on top of your actual job, this checklist is for you.
Across Pennsylvania, New Jersey, and Delaware, we work with growth-focused firms where cybersecurity responsibility lands on the wrong desk:
Finance directors, controllers, practice managers, operations leaders, none of whom signed up to run IT.
And yet… the pressure is rising.
- Your clients are asking for SOC 2 reports
- Your vendors are demanding NIST 800-171 or HIPAA alignment
- Your insurer is requiring MFA and endpoint monitoring
But there’s no internal CISO, and you’re not in a regulated industry. Yet.
That’s the danger zone. You’re expected to be compliant without a mandate, a budget, or a roadmap.
This checklist was built for:
- Multi-location healthcare practices
- CPA and advisory firms with high-net-worth clients or audit exposure
- Medical device, diagnostics, and specialty manufacturers under vendor-driven scrutiny
- GovCon-adjacent firms prepping for CMMC-like expectations
- Law firms handling sensitive litigation or financial data
- Any company where compliance matters but no one owns it
This is your plain-English starting point to identify gaps, reduce risk, and get back control before someone else decides you’re not ready.
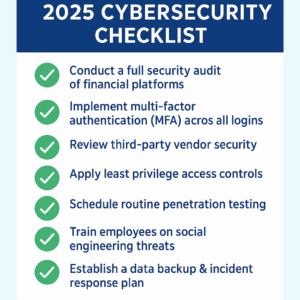
1. Audit All Financial, Clinical, or Operational Systems
QuickBooks, Sage, NetSuite, Athenahealth, or a custom ERP – it doesn’t matter what you use. Start by asking:
- Are there old user accounts that should be shut off?
- Is your software fully updated or are you months behind?
- Who has admin access and is it too many people?
- Any integrations or vendors with access you don’t control?
You don’t need to be technical to ask these questions. But if your vendor or internal IT can’t answer them, that’s your first red flag.
2. Turn On Multi-Factor Authentication (MFA)
MFA should be on everything:
- Accounting and billing systems
- EHRs
- File-sharing platforms
- Client or investor portals
We’ve worked with firms from Center City Philly to Wilmington that assumed MFA was on, until we showed them it wasn’t. It’s your first, easiest fix.
3. Ask Vendors for Proof of Security
If you’re outsourcing bookkeeping, billing, IT, cloud hosting, or data processing:
- Ask for their SOC 2 Type II report, or equivalent
- Confirm they have a documented incident response plan
- Ensure they meet your cyber liability insurer’s requirements
If they hedge or delay, you’re exposed.
- Lock Down Access with Least Privilege
Staff should only access what they need. Nothing more.
Ask yourself:
- Can the intern see payroll?
- Can marketing pull client data?
- Are logins being shared between front desk staff?
Least privilege limits how far an attacker or a mistake can spread.
5. Go Beyond Antivirus. Run a Pen Test
Antivirus isn’t enough. You need to simulate an actual attack.
A third-party penetration test helps uncover:
- Misconfigured firewalls
- Unpatched vulnerabilities
- Unknown entry points from third-party tools
It’s not about fear, it’s about clarity. We help clients across PA, NJ, and DE schedule, interpret, and act on real-world testing.
6. Train Your Staff to Spot Social Engineering
Phishing emails, spoofed login pages, fake password resets are still the #1 way firms get breached.
According to the IBM X-Force Threat Intelligence Report, phishing accounted for over 40% of all cybersecurity incidents in professional services last year.
Your staff should know how to:
- Recognize common social engineering tactics
- Pause before clicking suspicious links
- Report attempts without shame or delay
Especially in multi-office environments, consistent training is your first human-layer defense.
7. Build a Real Backup and Recovery Plan
If ransomware hits, how long would it take to get back online?
Too many firms think they have backups until they try to restore one.
Check:
- Are your backups automated, encrypted, and tested regularly?
- Do they cover email, files, databases, and infrastructure?
- Can you restore within hours, not weeks?
We’ve seen firms in Cherry Hill and West Chester think they were protected until the recovery took three weeks. That’s not protection. That’s a false sense of security.
FAQ: Cybersecurity & Compliance Without a CIO
What if we’re not regulated but vendors keep asking for SOC 2 or HIPAA alignment?
You’re not alone. Many growth-stage firms face “compliance by association.” Clients, insurers, and vendors now expect strong cybersecurity posture even without legal requirements.
We already have an IT vendor, do we still need this?
Most IT vendors focus on tickets and tools. This checklist helps you assess whether your setup is actually secure, documented, and audit-ready, especially if no one is filling the CISO role.
Want to Know Where You Really Stand?
At Total Technology Resources, we support firms in the financial, healthcare, manufacturing, and legal sectors across Pennsylvania, New Jersey, and Delaware, especially those without internal IT command.
If you’re facing compliance pressure but don’t have a clear roadmap our COMMAND™ Clear engagement gives you:
- A baseline audit of where your risks actually are
- An analysis of what tools you already have (and aren’t using)
- A simple, prioritized plan to fix what matters most
No jargon. No scare tactics. No nickel-and-diming.
Just clarity, confidence, and a team that can take the weight off your shoulders.
[Book My COMMAND™ Clear Assessment]
Know where you stand. Know what to fix. Then let us take it from there.
—
Total Technology Resources has 20+ years of experience supporting finance, healthcare, and manufacturing firms under increasing compliance pressure. They specialize in helping multi-location, growth companies secure complex IT environments.
for a FREE Consultation!
